Course Resource
Computer Security Incident Investigation
At this morning’s stand-up meeting, SITREPS from the teams working on the Reveton incident response effort were presented. There were additional SITREPS from CISO managers and team leaders. From those reports, you learned the following:
Chief Information Security Officer (CISO): There has been a 10 percent increase in absenteeism within the CISO organization due to illness. The Help Desk, Web Development team, and Server Operations teams are missing key personnel which is impacting their operations. All personnel are accounted for except for one of the web developers and one member of the Server Operations team. Both have been absent for more than five days. Calls to their residences have gone unanswered. Human Resources has been notified and authorization has been obtained to enter the offices and access the desktop computers/laptops as required to support recovery efforts for the Reveton incident.
Desktop Operations team: The team leader reported that desktop support technicians have been deployed to reimage the desktop computers and laptops affected by the Reveton malware. They estimate it will take at least three more days to clean and restore each of the affected laptops.
Digital Investigations team: This is a newly formed team, and the CISO welcomed them to their first stand-up. The team’s digital forensics technicians are working with the Desktop Operations team to collect evidence related to the Reveton infection. The technicians are following a strict protocol in which they first create an image backup for each affected storage device and system. After the forensic (image) backup has been made, a desktop technician will be tasked with restoring the operating system and user files from “known good” backups. Under the investigations protocol, a chain-of-custody document will be prepared for each set of image files and all investigation related documentation, including backup media, will be stored in a fire safe that has been repurposed to serve as an evidence locker.
Malware team: The malware analysts began their investigation immediately after the first users reported seeing the Reveton splash screen. The team has received copies of the image backups from a sampling of infected systems (provided by the forensics technicians). The analysts are continuing their study of the encrypted files found on the affected systems. The team lead expressed confidence that their efforts will lead to the identification of the attack vector allowing them to authoritatively answer the questions of “how the attackers infiltrated the system” and “how the malware was planted.” The malware team is also working with external threat tracking organizations. Of concern to the team and their external contacts is the fact that Reveton is a relatively old piece of malware originally seen in 2012. There are few if any reports of other organizations being infected with this malware.
Server Operations team: While performing scheduled maintenance on server hardware, maintenance personnel found a USB storage device (thumb drive) lying inside the rear panel of one of the hardware enclosures. The USB did not have external labels. This particular server hosts websites for both internal and external users. The team also found evidence in the log files that a new Windows 10 user account was recently created on that server. This new account was not properly authorized through the account management process.
Web Development team: The team leader noted that configuration control had been lost and files updated without required documentation for the web server where development is done for the Global Economic Summit web portal. This portal is an internal server that was designated for use in supporting conference organizers and attendees at the Global Economic Summit. The team has restored the web server and content files from a known good backup.
Decisions from the Stand-Up and Items Moving Forward
Supervisors for absent/missing personnel will accompany desktop technicians entering offices of absent personnel for the purposes of inspecting desktop computers and laptops. The current state of the office(s) will be documented using voice memos or written notes. Documentation will include photographs of the office/work area and physical desktop.
Server Operations team will transfer custody of the “found” USB storage device to the Digital Investigations team.
Digital Investigations team will assign staff to copy and then inspect the USB storage devices found by the Server Operations team. A digital image file of each device will be provided to the Malware team. The team will also investigate the unexpected user account found on the same server.
Malware Team will accept custody of a copy of the USB device and inspect it for evidence of malware.
An ad hoc incident response unit will be stood-up by the chief of staff’s office to assist with the investigation. You and your team have been assigned to this unit.
Your task
The Chief of Staff (CoS) has asked your team to review the information provided by several other teams as it is submitted to the CoS’s office. The first team to report in was the Human Resources team. Its report was followed by a report from the Digital Investigations team. The remaining teams have asked for additional time before making a report. The CoS has decided that you and your teammates should write a situation report
(https://www.thepersimmongroup.com/situation-report-sitrep-template/) for the next CISO standup meeting using the inputs from the two teams that have reported in.
Report from Human Resources Team
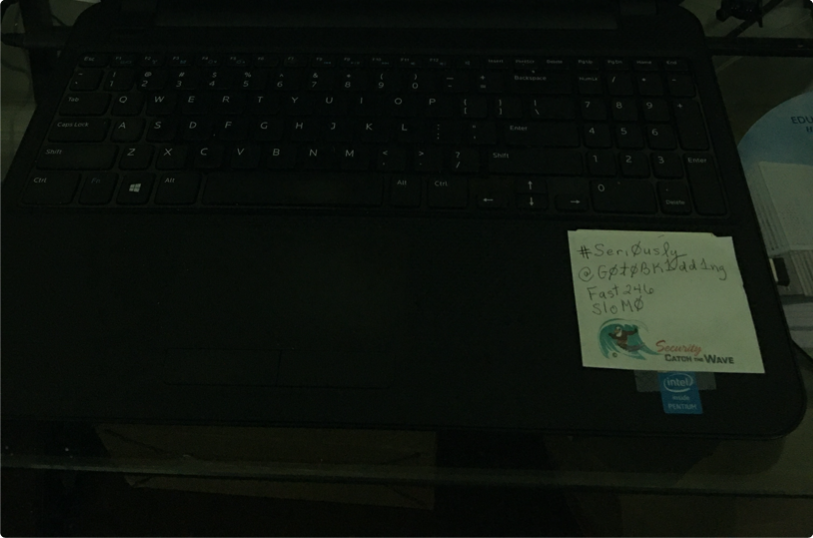
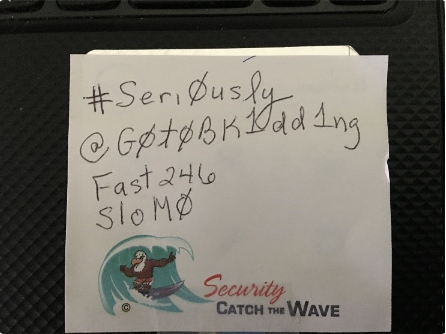
The Human Resources Office sent a representative to accompany supervisors as they entered the workspaces of the absent Web Developer team member and the absent Server Operations team member. The team members found a possible security violation in one of the offices—a list of what appear to be passwords taped to the laptop but only visible when it was opened. The team also found four USB removable storage devices scattered on the mouse pad. The supervisor confirmed that the laptop was last assigned to Penelope Anne Grascholtz. The workstation, however, is in an open cubicle area and could be accessed by anyone. A nearby employee commented that the laptop was frequently used by others on the Server Operations team. He seemed surprised that anyone would think the laptop was exclusively used by Ms. Grascholtz.

Report from Digital Investigations Team
Digital forensics professionals frequently serve organizations in roles related to security and risk management (https://leocontent.umgc.edu/content/scor/uncurated/cyb/2215cyb670/learning-topic-list/security-and-risk-management.html?ou=689272) and security assessment and testing
(https://leocontent.umgc.edu/content/scor/uncurated/cyb/2215-cyb670/learning-topiclist/security-assessment-and-testing.html?ou=689272) . Their responsibilities are focused not upon criminal investigations but rather upon using their expertise and tools to help the organization respond to incidents which adversely impact business operations.
However, digital forensics professionals are also trained investigators who must bring a level of open-mindedness to a situation and a willingness to challenge assumptions. Digital forensics investigations can require a significant amount of time due to the large amount of data the investigators must sift through. But, when necessary, the investigators can provide “quick look” reports to inform and collaborate with other investigators and incident responders.
As you work through the activities in this lab, you should follow the example of the digital forensics team and adopt a level of skepticism with respect to assumptions made both in the CISO’s organization and within your team.
Technicians working for the Digital Investigations team completed a “quick look” at both the USB storage device found in the back of the server cabinet and the presence of an unauthorized user account on the same machine. The Digital Investigations team’s formal investigative report is not yet ready. But that team did provide your team with the following information:
The user name for the unauthorized account was Penelope Anne
The account was a standard user account.
The system log files showed no privilege escalation for the Penelope Anne account.
The default browser for the Penelope Anne account was Firefox.
The Digital Investigations team leader provided your team with a list of URLs found in the browser history for the Penelope Anne account and suggested that you review those websites and web pages. He hinted that your SITREP should include a brief summary of what you learned from the browser history.
URL websites to review:
- https://www.google.com (https://www.google.com)
- https://www.facebook.com
- https://www.ic3.gov/complaint/default.aspx
(https://www.ic3.gov/complaint/default.aspx)
- https://www.ic3.gov/default.aspx (https://www.ic3.gov/default.aspx)
- https://www.ic3.gov/complaint/splash.aspx
(https://www.ic3.gov/complaint/splash.aspx)
- https://www.fbi.gov/coronavirus (https://www.fbi.gov/coronavirus)
- https://www.fbi.gov/news/stories/new-internet-scam
(https://www.fbi.gov/news/stories/new-internet-scam)
- https://www.justice.gov/opa/pr/washington-state-man-sentenced-prison-roleconnection-reveton-ransomware (https://www.justice.gov/opa/pr/washington-stateman-sentenced-prison-role-connection-reveton-ransomware)
- https://www.google.com/search?client=firefox-b-1-d&q=reveton+site=%3Afbi.gov
(https://www.google.com/search?client=firefox-b-1-d&q=reveton+site=%3Afbi.gov)
- https://www.zdnet.com/article/reveton-ransomware-distributor-sentenced-to-sixyears-in-prison-in-the-uk/ (https://www.zdnet.com/article/reveton-ransomwaredistributor-sentenced-to-six-years-in-prison-in-the-uk/)
- https://www.us-cert.gov/Ransomware (https://www.us-cert.gov/Ransomware)
- https://www.us-cert.gov/sites/default/files/2019-08/CISA_InsightsRansomware_Outbreak_S508C.pdf (https://www.uscert.gov/sites/default/files/2019-08/CISA_InsightsRansomware_Outbreak_S508C.pdf)
- https://www.cdc.gov/coronavirus/2019-ncov/index.html
(https://www.cdc.gov/coronavirus/2019-ncov/index.html)
- https://www.cdc.gov/coronavirus/2019-ncov/daily-life-coping/index.html
(https://www.cdc.gov/coronavirus/2019-ncov/daily-life-coping/index.html)
- https://www.cdc.gov/coronavirus/2019-ncov/travelers/index.html
(https://www.cdc.gov/coronavirus/2019-ncov/travelers/index.html)
- https://www.cdc.gov/coronavirus/2019-ncov/testing/index.html
(https://www.cdc.gov/coronavirus/2019-ncov/testing/index.html)
- https://www.hg.org/legal-articles/blackmail-or-extortion-what-to-do-when-policerefuse-to-get-involved-48226 (https://www.hg.org/legal-articles/blackmail-orextortion-what-to-do-when-police-refuse-to-get-involved-48226)
The Digital Investigations team leader also authorized release of a copy of a Microsoft
Word document to your team. The document appears to be a letter of resignation
(https://leocontent.umgc.edu/content/dam/course-content/tgs/cyb/cyb-
670/document/ToWhomItMayConcern.docx?ou=689272) found on the Windows 10 desktop of the unauthorized account. The file was password protected. Fortunately, the password was crackable using the team’s forensics software. The recovered password was: Fast246.
Did You Know?
Windows 10 stores information about a file (metadata) in an associated directory entry. You can view this information by opening a File Explorer window and then changing the view to “view details.” The available information includes last modified date, type, and size. If you right-click on the file name and select “Properties,” you will see additional metadata for the file.
Microsoft Word also stores information about a file (metadata) internal to the file. You can view this information by selecting the File tab and then choosing Info from the left-hand menu. The available information includes size, total editing time, last modified date, creation date, last printed date, author, and last editor (last modified by).
Both sources of metadata should be reviewed and compared when investigating incidents involving Microsoft Office files.
Toward the end of the meeting, the team’s forensics technician was asked about the USB storage device. To support her discussion, she showed two pictures on the room’s projection screen. The first was the USB device with its label “USB7.” The second was a screen snapshot taken during her inspection of the structure and digital contents of the device.
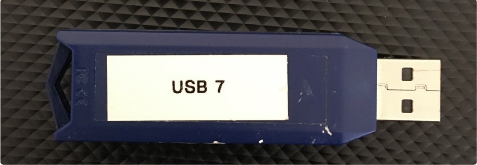
She then went on to report that her inspection of the USB found multiple partitions on the removable storage device.
The highlights of the technician’s findings are as follows:
Only the first partition had any data.
The other three partitions were zero-filled.
This type of partitioning is commonly used on hard drives to create multiple logical drives on a large physical drive.
Windows 10 will not allow partitioning of removable storage media.
People who “have something to hide” can use this “multiple partitions” technique to hide data on a USB since Windows 10 (and earlier Windows operating systems) will not allow direct access to the contents of those extra partitions.
The techniques and tools to create multiple partitions on a USB or other types of removable storage media is easily found on the internet.
The evidence technician provided your team with a copy of her Investigator’s Case notes (https://leocontent.umgc.edu/content/umuc/tgs/cyb/cyb670/2221/courseresource-list/investigator-case-notes.html?ou=689272) for your review.
Report Out With the Chief of Staff
Upon returning to the office, your team received a list of guiding questions from the CoS. You have been asked to address these questions when writing your SITREP from the information provided by the Human Resources and Digital Investigations teams.
- What actually happened? What do you know as fact?
- What was said in the letter of resignation? Can this document be trusted as representing the true intentions of Ms. Grascholtz? Why or why not?
- Several staff have commented that the USB devices found in Ms. Grascholtz’s work area are of the same type and brand as the USB found inside the server cabinet. Is this significant? Why or why not?
- What is the significance of the list of passwords found taped to the laptop?
- What is the significance of a multipartition USB storage device?
- What conclusions can be drawn from your analysis of the browsing history?
- Is there sufficient evidence to show a link between the Reveton malware and Ms.
Grascholtz?
- Is there evidence supporting the supposition that an insider other than Ms. Grascholtz may have been responsible for the Reveton malware’s entry onto the organization’s networks?
- What other conclusions can be drawn from the information you have at hand?
- What are the next steps that the CISO and staff should take to further this investigation into the Reveton malware?
© 2022 University of Maryland Global Campus
All links to external sites were verified at the time of publication. UMGC is not responsible for the validity or integrity of information located at external sites.